Tips & Tools
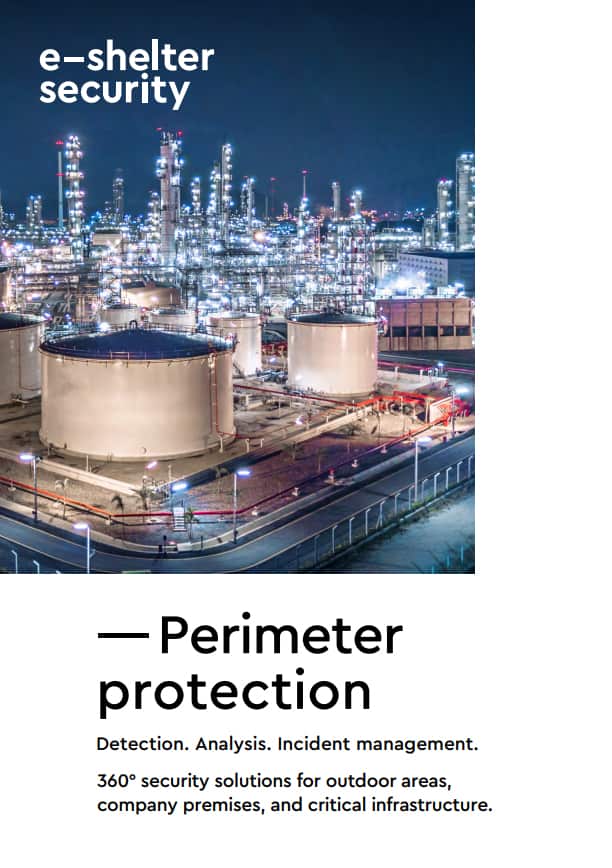
Protect your critical infrastructure more effectively against threats.
― Challenges
― Interaction
― Detection
― Analysis
― Incident management
Our team of experts is pleased to assist you
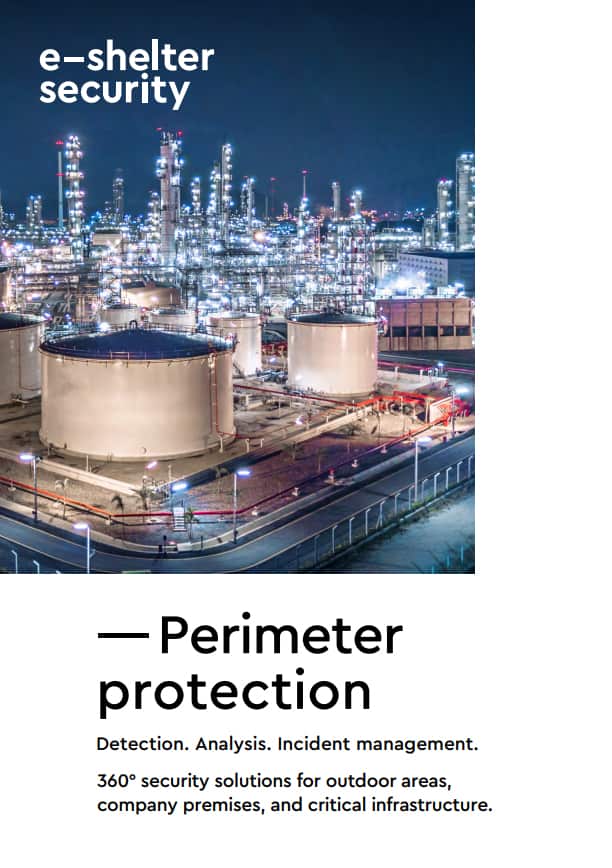
Protect your critical infrastructure more effectively against threats.
― Challenges
― Interaction
― Detection
― Analysis
― Incident management
Our team of experts is pleased to assist you
You need to load content from reCAPTCHA to submit the form. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Turnstile. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Facebook. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from Instagram. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More InformationYou are currently viewing a placeholder content from X. To access the actual content, click the button below. Please note that doing so will share data with third-party providers.
More Information